About the Project
Basics
Description
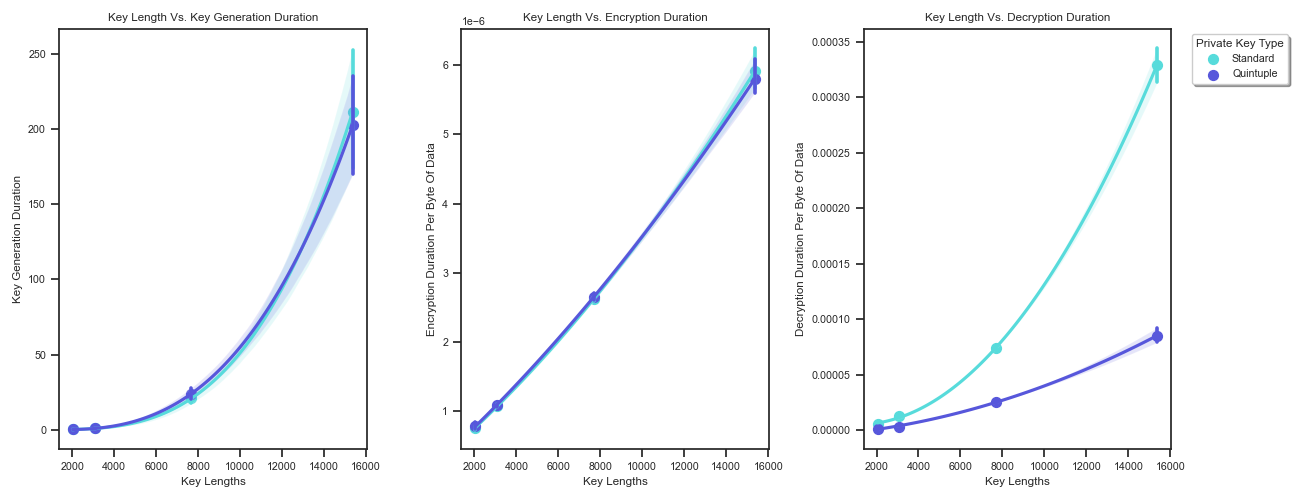
An exploration of cryptography and the algorithms that are used.
Programs are created following the relevant standards, such as NIST FIPS 186-5 and IETF RFC 8017 for RSA.
The algorithms have been coded in Python / C++, and the GUI application is written in C++ with QT.
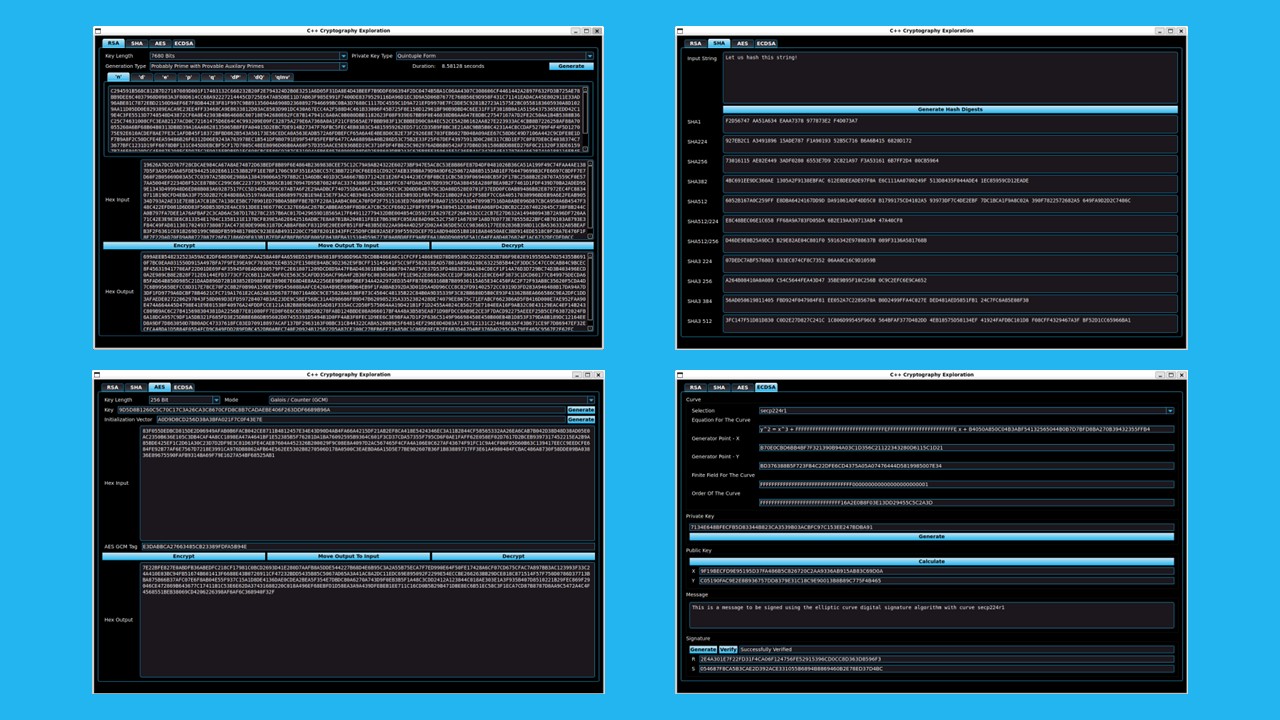
The GUI currently has four main tabs, "RSA", "SHA", "AES" and "ECDSA".
Technology Used
- Python
- C++
- QT
- unittest
- GTest
GUI Application
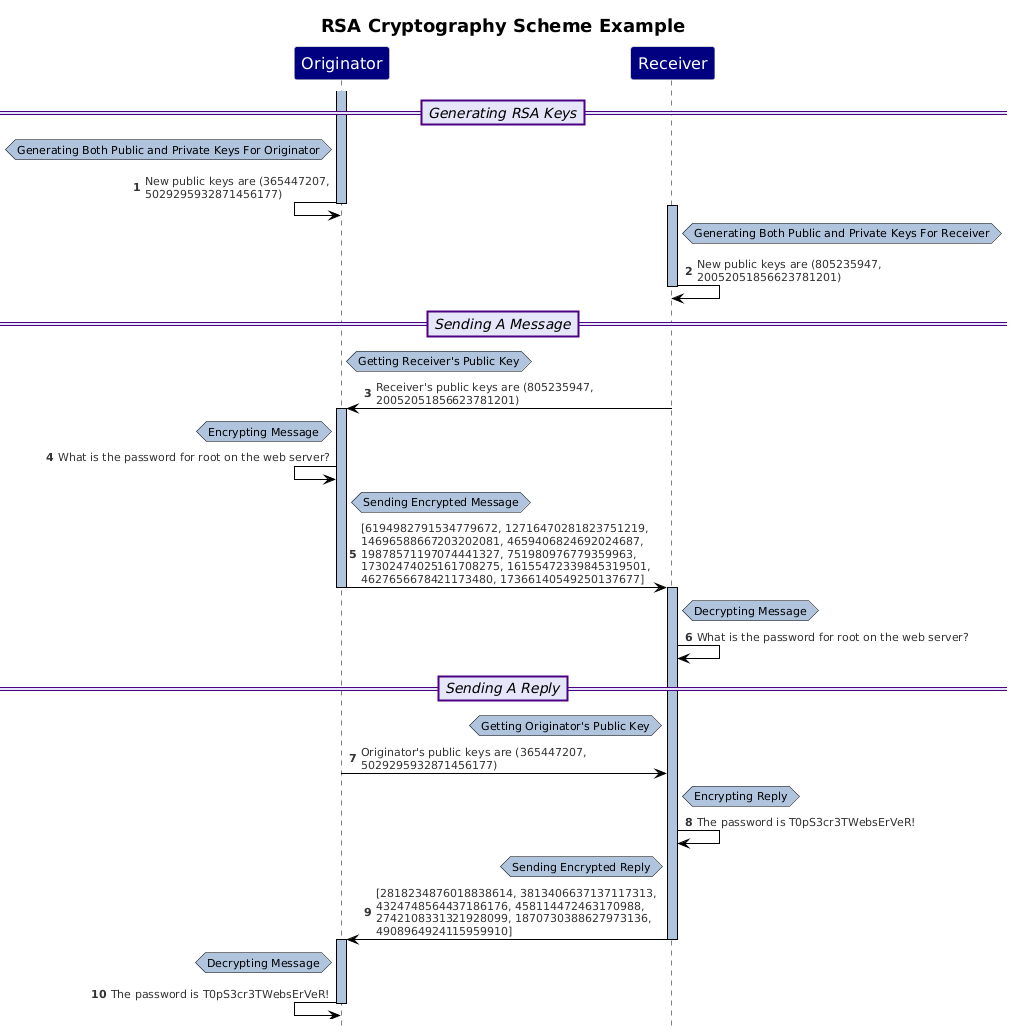
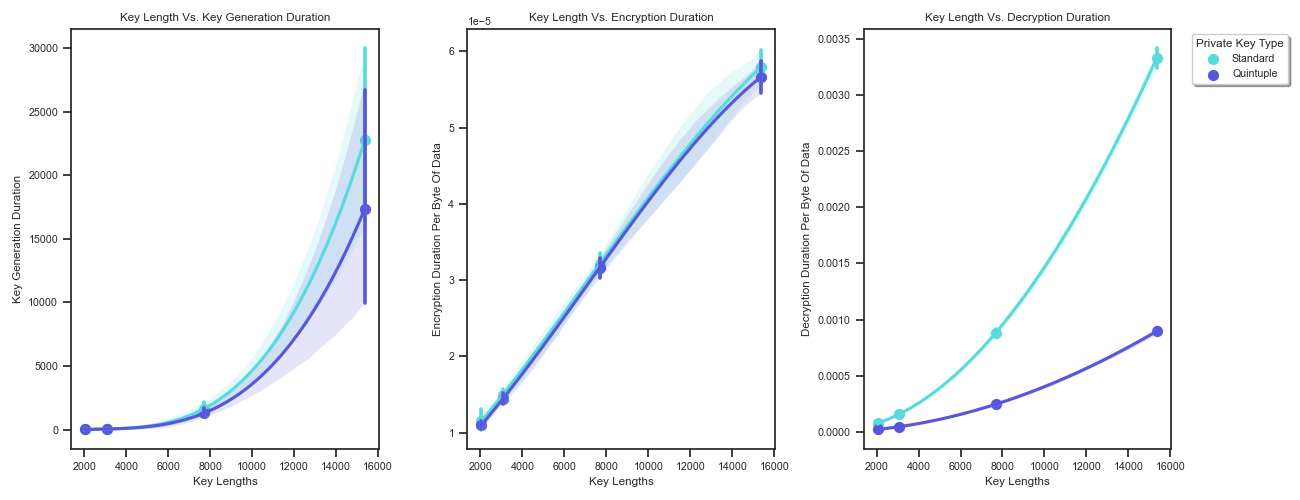
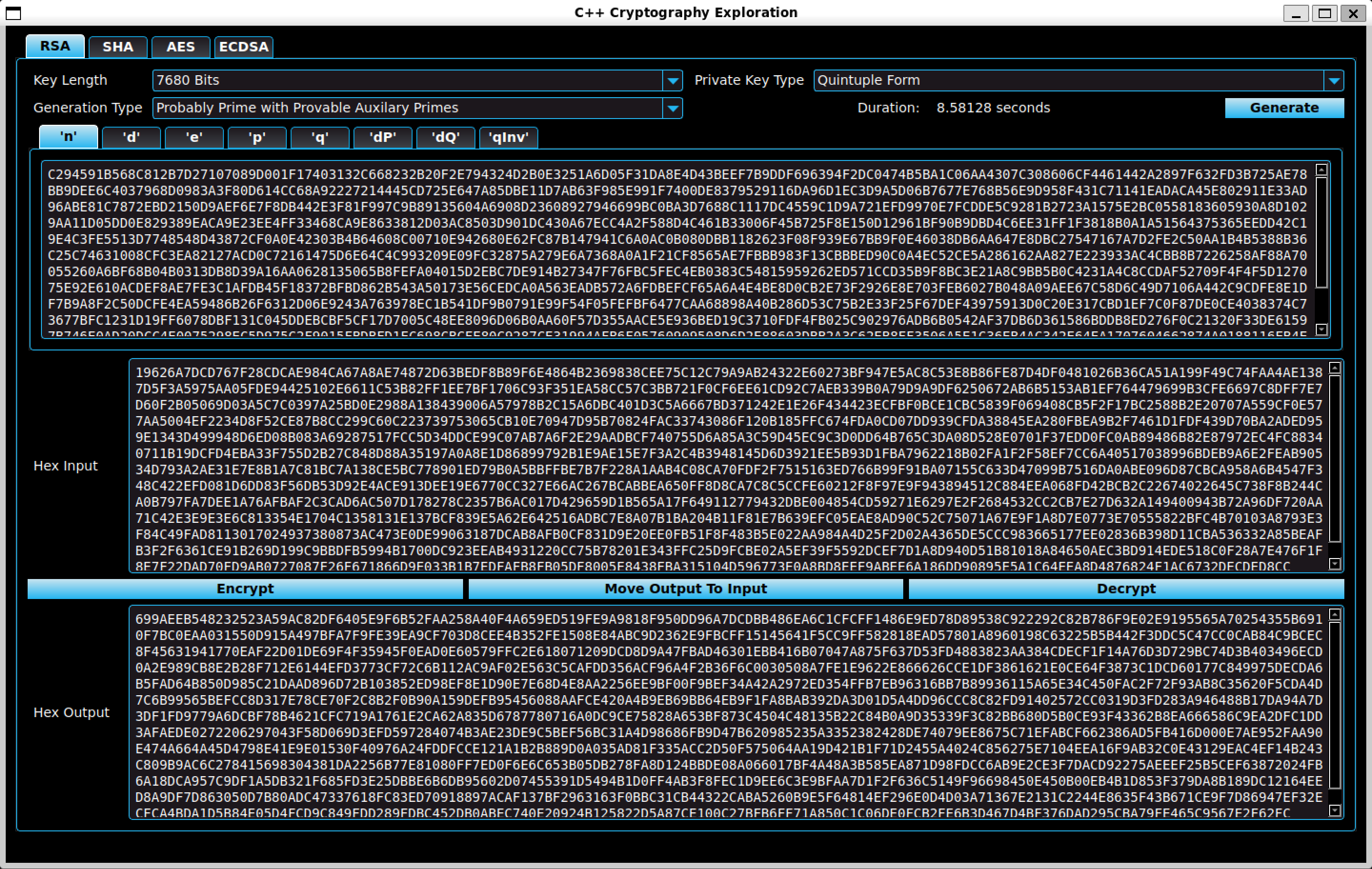
RSA
Rivest Shamir Adelman
The RSA tab allows the user to generate a pair of RSA keys and then use them to encrypt or decrypt hexadecimal strings.
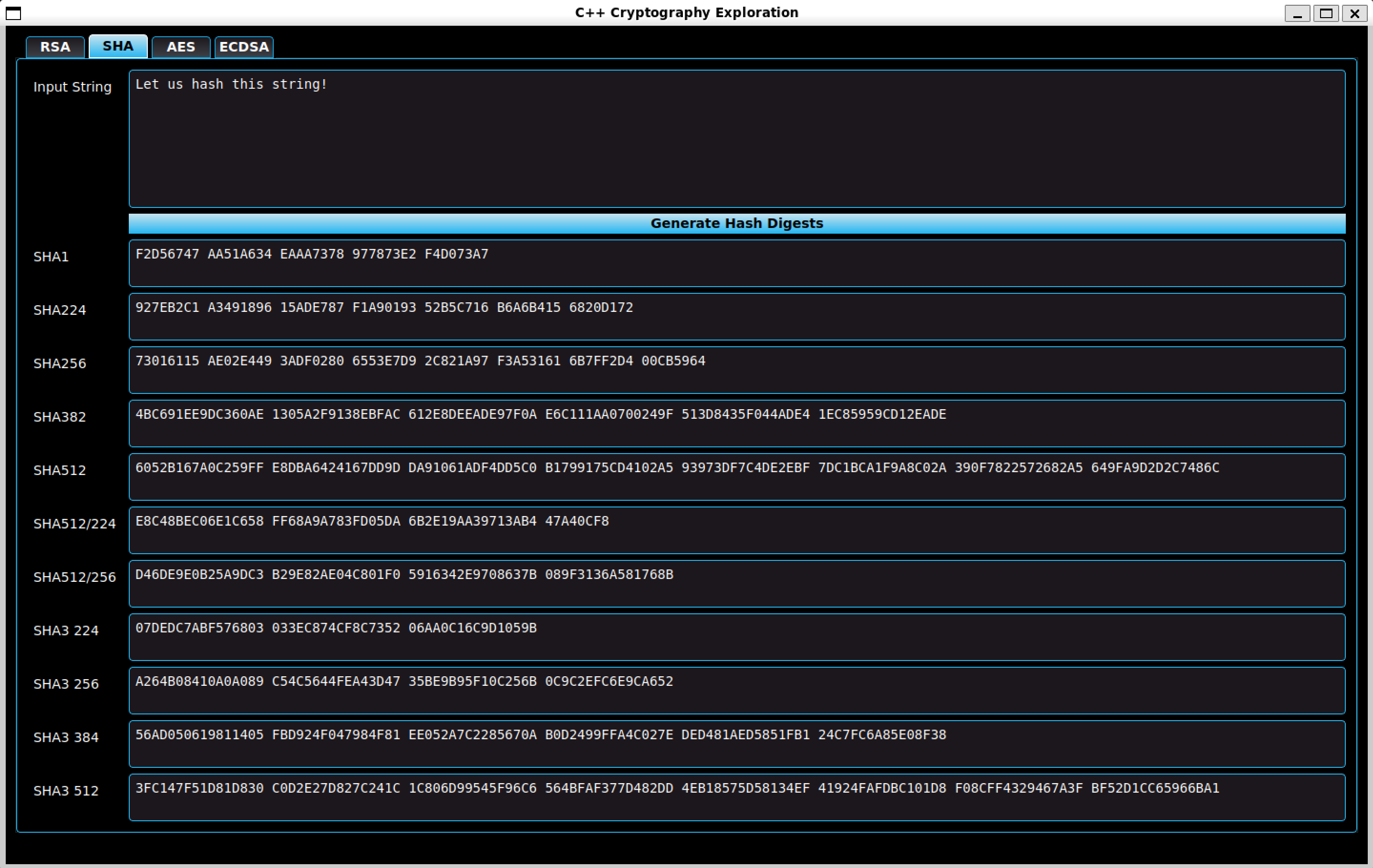
SHA
Secure Hash Algorithm
The SHA tab allows the user to enter a string of text and then generate the hash digests using SHA1, SHA2 and SHA3.
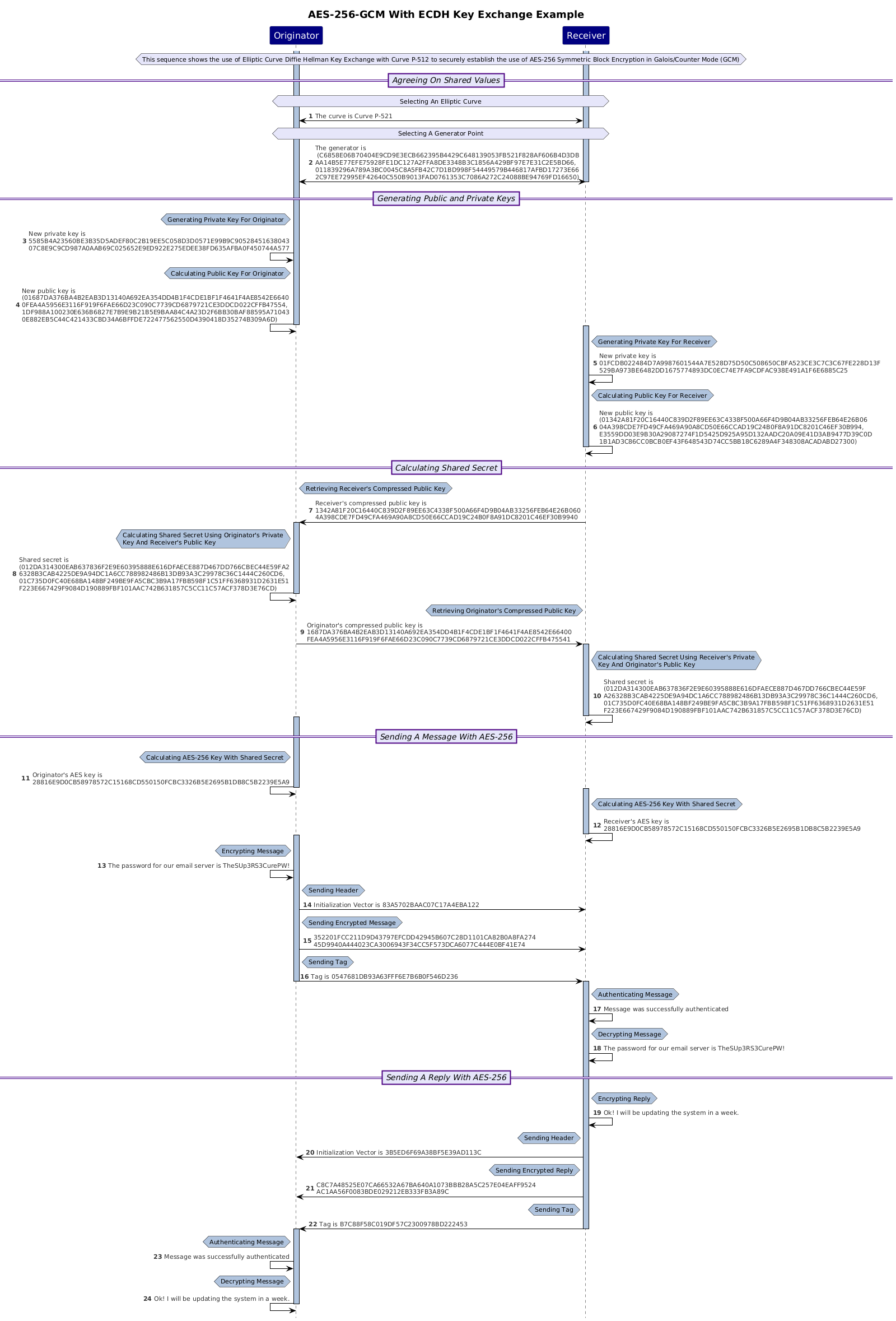
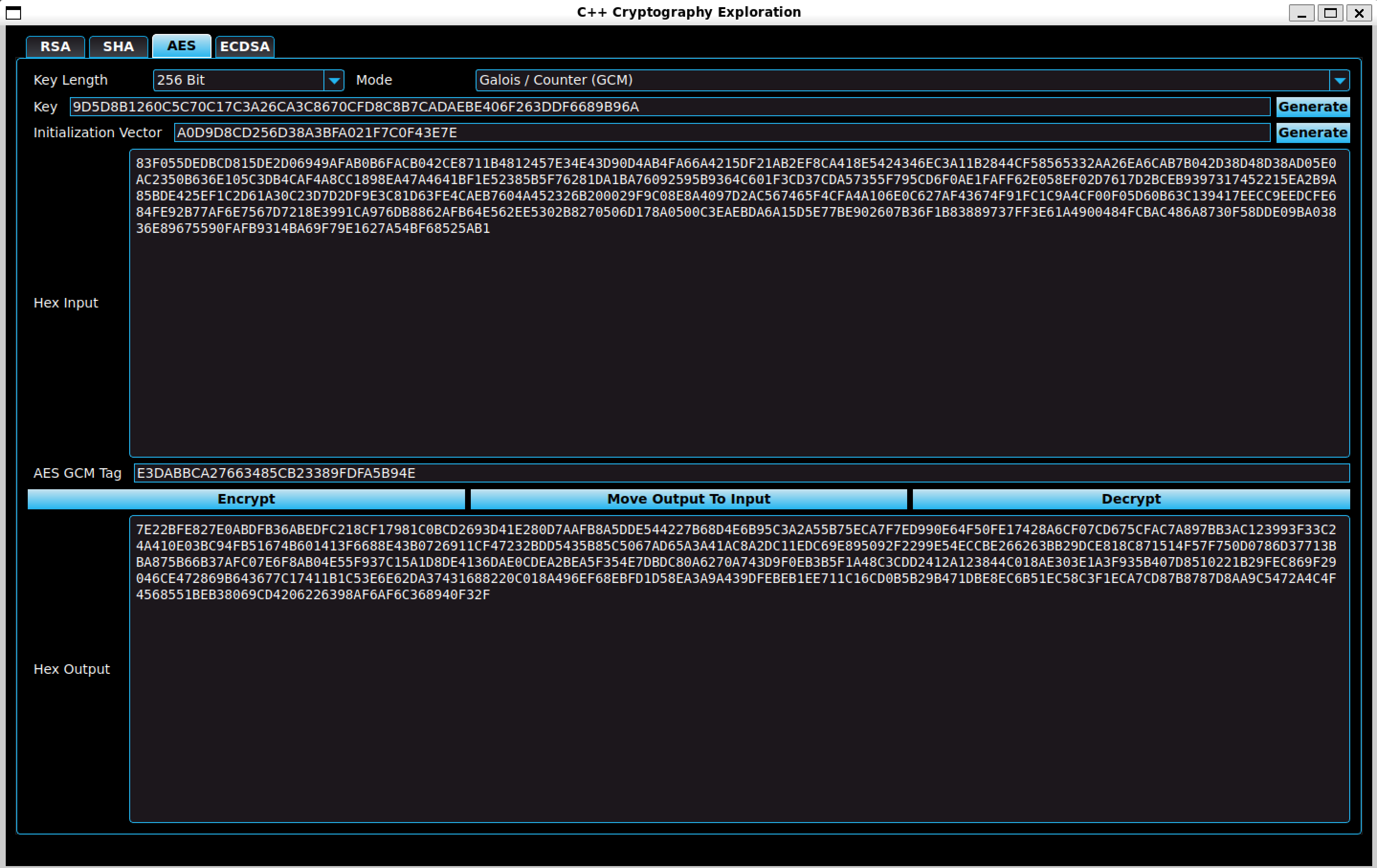
AES
Advanced Encryption Standard
The AES tab allows the user to enrypt and decrypt hexadecimal strings using various AES Modes selected using the dropdowns.
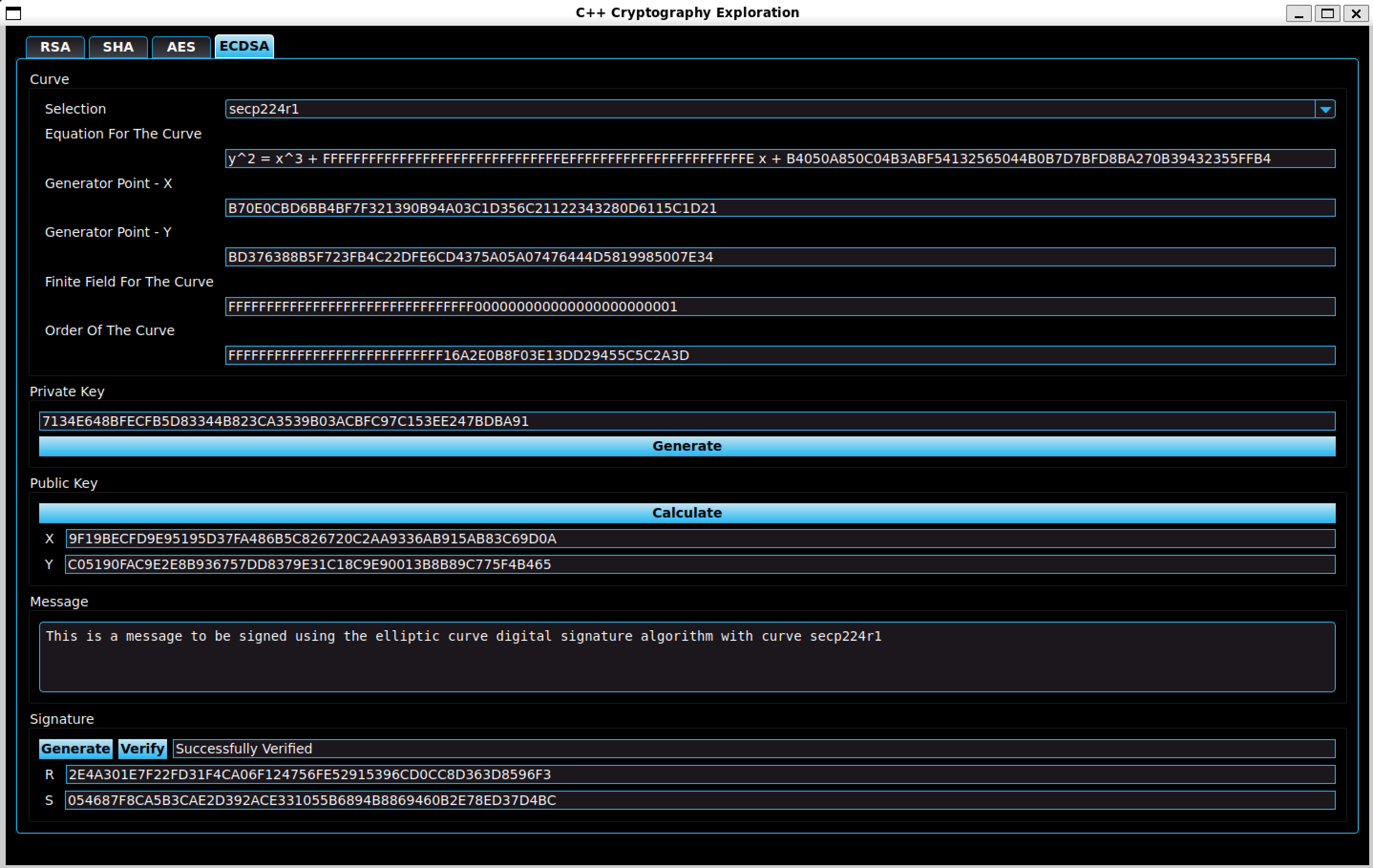
ECDSA
Elliptic Curve Digital Signature Algorithm
The ECDSA tab allows the user to enter a string of text and generate or verify the corresponding signature using the public and private keys.